WordPress is one of the most popular content management systems currently available. It is also a favorite vehicle for hackers to infiltrate websites and spread malware.
However, with a few simple precautions, you can prevent your WordPress website from being hacked.
Malware is any software that is intentionally designed to cause disruption to computers, servers, clients, or computer networks, leak private information, or gain unauthorized access to information. By contrast, software with a bug that causes harm is typically described as a software bug. Malware is a serious problem for individuals and businesses.
According to Symantec’s 2018 Internet Security Threat Report, the number of malware variants number has increased to 669,948,865 in 2017. 
There are many types of malware, including computer viruses, worms, Trojan horses, ransomware, spyware, adware, and rogue. The defense strategies against malicious software differ according to the type, but most can be thwarted with antivirus software, firewalls, applying regular patches, securing networks from intrusion, having regular backups, and isolating infected systems. Malware is now designed to evade antivirus detection algorithms.
Let’s take a look at a short explanation of these types of malware and their uses in malware attacks. After that, we’ll get to how to prevent malicious software attacks from being successful against you.
- Trojans. This kind of malware is often disguised as a software update or an app. When the software update has been installed, the malware is installed on your computer as well. A trojan horse can lead to other malware, including ransomware, crypto-mining malware, and spyware attacks.
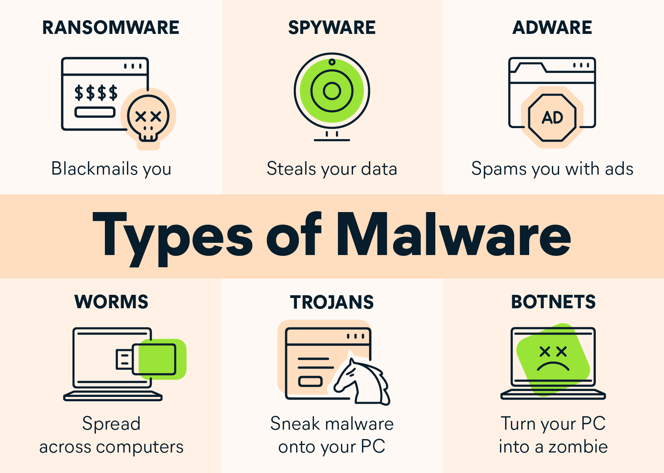
- Viruses. A virus is malware attacking the victim’s computer by piggybacking on other programs. When the host program is run, the virus is activated. After activation, a virus multiplies itself and spreads the infection within the computer. It is also programmed to send itself to other computers in the same network.
- Worms. A worm is a type of malware that does not require a human to activate it. A worm is quite dangerous as it can infect, multiply, and send itself to other computers. Due to this, worms spread quickly and are hard to stop.
- Spyware. Spyware is a category encompassing many types of malware. Cybercriminals use it to observe and record users’ behaviors and keystrokes to capture sensitive data (such as login credentials).
- Adware. Compared to others, adware is often considered a relatively harmless type of malware. Adware collects users’ data, including their browsing and search histories, shopping preferences, and cart details, to sell to advertisers or display targeted ads.
- Fileless Malware. Fileless malware does not have its own file for malicious code. It candidly attaches its malicious code to other programs. It is improbable to discover fileless malware due to this feature. This kind of malware often links its code to white-listed programs to avoid detection in a routine scan.
- Ransomware. A cybercriminal uses malware to encrypt victims’ data, devices, or IT systems to carry out a ransomware attack. They demand a ransom in exchange for a decryption key. In some cases, they’ll exfiltrate the data to a server they control to use as they please. Verizon describes ransomware as a “big problem getting bigger.”
- Cryptojacking Malware. Cybercriminals use cryptojacking malware to mine cryptocurrencies such as Bitcoin and Ethereum. They create a network of infected computers that run mining programs in the background without the user’s knowledge. As a result, the performance and processing capabilities of the victims’ devices will decrease drastically.
- Rootkits. A rootkit is a remote access tool (RAT), often malicious, that provides an attacker with remote administrative access to a target’s device, network, or other IT resources. The criminals can use this access to change or even pull down the infected website.
- Botnet malware. Cybercriminals sometimes infect the computer, not for the data stored on that computer but to use it as a puppet to commit some other crime. They build armies of such computers referred to as bots or zombies. These armies work for the criminals per se, or the criminals rent it to others to use maliciously. The bots or the zombie computers are unaware of them being used maliciouslyز
How To Know If My WordPress Site Was Hacked?
When a WordPress site gets hacked, its administrator certainly goes through a lot of headaches. After all, the more time that your site remains hacked, the greater the opportunities you will lose from possible new sales.
However, it is important to stay calm at this stage and try to figure out what the source of the hack is. This is essential if you are to find the solution to your problem. After all, there’s no way to build a successful solution without knowing beforehand how your problem came about, isn’t it true?
To do that, try to answer the following questions:
- Are your wp-admin login and password not working.
- Is your site redirecting to another (that doesn’t have anything to do with yours)?## Input:
- Does Google Analytics show access to unfamiliar content created on your website (most of it in other languages like Chinese)?
- Does Google Search Console point to your site as insecure?
If the answer to any of the questions is “yes,” it is a strong indication your site was hacked. In a worst-case scenario, all of these questions will be “yes.” It is important to pass this information on because, when contacting your hosting server, such information must always be passed on.
What Are The Reasons That Make A WordPress Site Hacked?
There are four points that justify what may have caused the invasion of a WordPress site.
1. Easy Identification
WordPress is one of the most used content management systems in the world, besides being very easy to identify if a website is built on the platform
Do you want to learn how? To access the Developer Tools, go to any site in Google Chrome and click on the three dots in the top right corner. Then, choose “More tools” and then ” Developer Tools”.
If the site’s URL contains “wp-content”, it’s built on WordPress, and this can make it a potential “victim” if the proper precautions ― which we’ll talk about later ― are not taken.
2. Open-Source
The fact WordPress is an open-source platform that allows you to embed functionalities that meet your needs, like plugins and widgets.
However, having the source code change to anyone gives hackers a chance to exploit any loopholes in your site.
3. Theme And Plugins
Anyone who knows programming is able to create a plugin and make it available on WordPress Therefore, we stress that you should only install plugins from reliable sources. Some programs are created to open the path for invasion.
4. Manual Updates
WordPress, as well as the themes and plugins it uses, may not automatically perform upgrades, forcing the user to manually do it.
If your site does receive the updates, it may become vulnerable.
How To Identify Infected Files?
Assuming your site has lots of files, including images, text, and videos, how do you know which files have been infected by the malicious software? There are two ways you can do so: checking the time and the log.
The data check is a way of looking at the history of a website to see if new files were added or if any files were modified.
For example, if the website was working properly on the 5th and no files were published before the 10th, and on the 7th, files were added or modified but the website was still working normally, it means that the attack probably happened on that day.
Another way to do it is through the log. It will pinpoint where an attack came from by identifying the IP address that was used to invade your website and make changes to it, and it will also tell you which IP address was used to make the changes.
By knowing which path the attacker took, it becomes possible not just to restore the site, it also becomes possible to protect it from future attacks coming from that same source
Preventing Your WordPress Site From Being Hacked
Now that you know what a WordPress site can be attacked, let’s look at what you should do if it happens to your site.
Contact The Hosting Company
Most companies that offer website hosting services are prepared to deal with such issues. After all, those operating such a service need to have a good knowledge of the subject so they can help you solve a serious problem.
Moreover, if your website is shared with other websites that use the same service, the hack may also affect those websites.
For this reason, it is important that customer support can point out the origin of an attack and, if necessary, can quarantine your site to avoid causing damage to the server or its users.
This kind of technical support is usually performed by chat, email, or phone. Many companies restrict themselves by informing the client, being up to the customer to solve the problem on his or her own, which can complicate resolution.
That is why inStage, a solution that Fix Hacked Site for creating WordPress sites focused only on results, the support is dedicated not just to identifying the root of a problem but also to guiding users on how to solve it.
Create A Backup
Backups are something you should do on an hourly, daily, weekly, or two-weekly basis, depending on the size of your data.
It is essential for blogs to post a lot of content because it would be a pity to write articles that take a lot of work to simply lose them.
So, when hiring hosting servers, remember to ask how frequently the backup is performed (for example, in Rock Stage, it’s once a week). You can also count upon backup plugins on WordPress to help you go back to the recovery state before the hack happened.
Restore The Backup
Once you have built your backup, the next step will be to restore it. We reinforce the alert you may have been hacked before creating the backup, that is you will lose all posts and modifications made before the attack.
If you have chosen the restore option, the support team can restore your site and your settings will return to the way they were before the hack.
Therefore, we suggest that you save your site’s textual content also externally — as in Google Drive — so that they are posted again if such a situation occurs.
After the restore is done, observe how your site performs and if the errors it was displaying are gone.
After all, in the same way, that you can publish blog posts with retroactive dates, hackers can also manipulate the date a file was modified. So it the importance of making sure everything is ok.
Change Your Login And Password
After following the steps, it is also highly recommended that you change your login password, especially if you haven’t been able to identify how hackers have managed to break into your website.
For this reason, the WordPress team recommends that you always choose strong passwords.
After all, some attacks occur after the hacker has already programmed a bot to make multiple attempts to access the site, making weak password sites vulnerable to attacks.
How To Prevent My Site From Being Hacked?
If your site has never been hacked, this is great! However, that does not mean that you should be less careful. It can really happen to anyone. So, follow the steps below to improve the security of your website.
Keep Your WordPress Site Updated 
One of the safest and easiest ways to keep WordPress up-to-date is to keep it always up-to-date.
When a WordPress update needs to be installed, a message appears on the dashboard’s home page. Since this is the screen you see every time you log in to the platform, you will certainly not forget to update it.
When it comes to themes and plugins, you’ll probably need to check each one individually. For this, just go to “Appearance / Theming” to check if any of them need to be updated.
To give you an example, around 35% of all WordPress installations are outdated, which means it’s important that you check your website to make sure that all features are working.
Get An SSL Certificate 
SSL certificates are used to transform non-secured (HTTP-initiating) websites into secured (whose URLs start with HTTPS). Currently, most servers provide this certificate for free, all you need to do is request it.
This is essential not only for visitors to know that your site is secure, but also because search engines take into account security as one of the criteria they use to position your site in their search results.
Ensure That Your System Monitors Firewalls
The firewall is a device that controls the transfer of data. It allows only those who are authorized to transfer data. Therefore, make sure your hosting server provides this feature, too.
Give Preference To The WordPress Platform
Even though said that the CMS has vulnerabilities, they occur if you don’t do what we’ve pointed out throughout this post.
After all, WordPress has been one of the most secure websites there is, starting with its security features such as Really Secure SSL.
Count On Two-Factor Authentication 
Two-factor authentication is a process that makes your website login stronger. Through it, besides entering your username and password, you also have to authenticate your entry through an application, token, magnetic card, SMS, or email, and you can do this in a variety of ways.
Of course, this means that the login process takes longer, but on the positive side, it increases your website’s connection security, making any form of invasion extremely unlikely to occur.
By following these tips to keep your WordPress site safe, the chances of having it hacked decrease dramatically. So, you can focus your attention on managing your online strategies based on them.
This is why having a strong cyber-defense and cyber-aware workforce and users is critical. By following strict preventive methods and educating users, you may be able to reduce the chances of malware and scam techniques being successful against you.
For even more protection, check out Fix Hacked Site. This website security checker scans your site for malware, removing it automatically and protecting your site from attack.