This article is exclusively about website security risks so that we will talk about the most critical security risks for business websites today.
Top 10 Most Critical security risks For business websites
Your business website is beautiful. It is effective. It constantly brings new visitors to your business. But it can also be a liability if it’s not secure. To stay safe, it’s essential to know the most common security risks for business websites.
We’ve all seen what happens in the business world when confidential information is compromised. And it’s not pretty. While not the most glamorous topic, web security is perhaps one of the most important to address when working on your business website.
Security can be a complex topic, especially if you’re not a web developer. Still, it’s essential to understand the basics to ensure your web provider takes care of you and your customers the way you expect.
So, where can we start?
The first step is to identify that there are several security risks to business websites, small businesses. It’s very easy to think that only large companies like Amazon, Target, and the like are in the crosshairs of attackers.
Yet even if your business is small doesn’t mean it’s not a Target.
A major misconception about security threats is that hackers are explicitly attacking your website directly. In reality, they are attacking the application that supports your website.
Not all of the application risks we discuss here will apply to your business. Most websites are supported by a CMS or Web Application, and some of these applications are more secure than others. But as a general rule, the more custom applications you use (CMS, CRM, etc.), the greater the security risks to enterprise websites.
How is Risk Assessed, Anyways?
In what ways can security risks compromise your website?
The Open Web Application Security Project (OWASP) is an “open community designed to enable organizations to develop, acquire, and maintain trusted applications and APIs.”
The organization keeps an eye on critical threats and provides advice to developers around the world. They also offer numerous free resources to support the mission of an open and secure web.
One of those resources is the Top 10 security risks document, which was revised in 2017. In it, they take a comprehensive look at the top 10 security risks for websites. If you don’t have the time to study Software Engineering, we thought we’d break them down and explain why they are essential.
There are four basic dimensions to consider when analyzing security risks for enterprise websites:
Exploitability– How easy it is for a hacker to carry out the attack (1: Difficult to Exploit, 3 Easy to Exploit)
Prevalence– How commonly this attack vector is used (1: Uncommon, 3: Widespread)
Ease of detection– How difficult is it to recognize a threat to this attack vector (1: Difficult to detect, 3 Easy to detect)
Technical Impact– How much havoc this attack can wreak (1: minor impact, 3: severe impact)
Let’s get into the specific security risks for business websites:
Risk #1: Injection Flaws
The web works through requests and data transfers. The code in the Browser, on a server, in a database, etc. is responsible for forwarding requests and data from one entity to another.
An injection fault occurs when an attacker misuses these commands to send untrusted data into a system. This causes the system to execute unintended commands or access data without being authorized to do so.
This happens quite frequently. It is easy to exploit. And it can seriously compromise your system. For example, WordPress had a significant vulnerability that exposed tens of thousands of websites to the risk of a website hijack.
The solution? If you’re not a developer, the best thing you can do is an update. Software developers are continuously on the lookout for bugs in their code or vulnerabilities they may have missed. When they find bugs or vulnerabilities, they release patches to close them.
Keeping your software up-to-date reduces the risk of injection attacks because it reflects the patches implemented by the developers. The older an application is, the more likely it is that an attacker knows how to exploit it in its database.
Risk #2: Broken Authentication
Do your customers have accounts on your site? When your customers sign in, you authenticate their identity. You prove they are who they say they are and ensure that your private data is confidential.
If authentication is weak or flawed, hackers can assume the identity of someone in that system. They can pretend to be the authenticated user and perform all sorts of fraudulent activities.
In reality, attackers have access to hundreds of millions of valid username and password combinations. (And as we know, lots of people don’t update their passwords regularly. This is where a password manager can help.)
They can create fraudulent default administrator accounts. They have automated tools to hack systems and good eyes to manually discover vulnerabilities on websites where they should use these automated tools.
And they might only need access to one account to infiltrate your system.
To protect against these types of attacks, you should set up multi-level authentication whenever possible. The more hurdles an attacker has to overcome, the harder it is to get into your system.
Also, pay attention to session management and set application time limits correctly. When a user closes their Browser, log them out of the system. Any time a user leaves a session while still logged in, the entire system remains vulnerable.
Risk #3: Sensitive Data Exposure
The most common and consequential attacks have occurred in the last five years by simply exposing too much sensitive data. Software that shares sensitive information via sessions, URLs, or poorly constructed code increases the risk of vulnerability.
While most small business owners don’t have to worry about URL design, you should ask some questions if you see the personal information in a Browser URL.
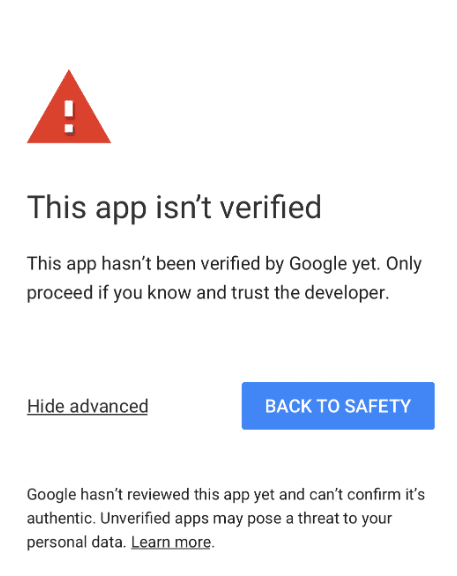
Also, watch out for mismatched keys, which may indicate that the site you’re trying to access and the site you’re authenticating to is different. Have you ever seen the “This application cannot be trusted” notice on Google?
Risk #4: XML External Entities
XML processors evaluate/process external references in XML documents when making requests. If these processors are compromised, we can use them to expose sensitive internal files.
This is a significant risk factor for developers but is usually not relevant for small business websites unless you use many custom programs. If you use custom programs, make sure your web developer and support service are aware of these issues.
Risk #5: Broken Access Control
It is important to control who has access to which parts of your website. This is not to be confused with the broken access mentioned above.
For example, let’s say you give a contractor administrator rights to your website.
Did you remove that access when he was no longer working for you? What about your Google information? Your email service?
The more expired but valid access points you have to your system, the more vulnerable you are to attack. attackers can get into your system and change your data without you knowing it. And employees who have too much access can break something, intentionally or unintentionally. So make sure you always know who has access!
Risk #6: Security Misconfiguration
Let’s say you buy a router. Or a printer. Or a shared storage system, cloud-based or not. This new component came with a default username and password. Let’s assume you set it up and didn’t change the password.
If an attacker has a list of default usernames and passwords at hand, they can break right into your system.
Please make sure you change your passwords and keep them up to date. If you leave insecure default configurations on your system, you can get into trouble.
Risk #7- Cross-Site Scripting
Let’s imagine for a moment that your site can act as an unwitting accomplice for an attacker. When a visitor gets to your site, the attacker uses your website to execute scripts in the victim’s Browser, hijack user sessions, and redirect visitors to malicious websites.
Unfortunately, you don’t have to imagine it: This threat is all too real.
When attackers use cross-site scripting, they intercept the user’s cookies and sensitive data, redirect traffic, and can even change your existing page!
There are methods to prevent this, from using secure forms to coding the site so that visiting Browsers can only interpret the data and not modify it. Make sure the support team for your site knows these ways to reduce the risk.
Risk #8- Insecure Deserialization
Converting data into a stream of bytes for storage or transmission is called serialization. If your website’s serialization is insecure, the underlying code serializes and transmits the data inappropriately. If the wrong people get your data, bad things can happen.
Since this is difficult to exploit from the outside, it’s not high on the radar of most small business websites. Just make sure your software uses good serialization practices.
Risk #9- Using Components With Known vulnerabilities
Your website is only as secure as the components it uses.
When installing libraries, plugins, frameworks, and the like, make sure they are updated and verified. As we mention in our ultimate guide to securing your business website, most users reach for free, open-source options for themes and plugins. However, free components may not be updated as often and are therefore more vulnerable to attacks.
If you install an insecure component, you put the entire website at risk.
This risk can be especially acute if you’re using a self-hosted CMS (like WordPress!) and using plugins to add custom functionality. So, make sure your web developer/support team adequately vets the components and gives them proper access to your system.
Risk #10- Insufficient Logging & Monitoring
If your website does not log information consistently and those logs are not monitored consistently, you will not know if attackers have entered your system. If attackers do access your system, they may remain there and even infiltrate another system.
Only accurate logging and a consistent response can ensure that your system has not been attacked. The more detailed the logging and the better the monitoring, the greater the chances of quickly detecting deviant behavior. So once again, make sure your website is monitored and supported!
Have you checked out our Free 25 Point Website Vulnerability and Performance Optimization Check?
It helps ensure your website is in tip-top shape. And it is free! Check it out now here: Free 25 Point Website Vulnerability and Performance Optimization Check
Read More: Top Security Tips to Build a Trusted Website



